If you’ve recently issued a new SSL/TLS certificate and noticed the expiration date is much sooner than expected, you aren’t alone. As of March 15, 2026, the industry has officially moved away from the 398-day (one-year) standard.
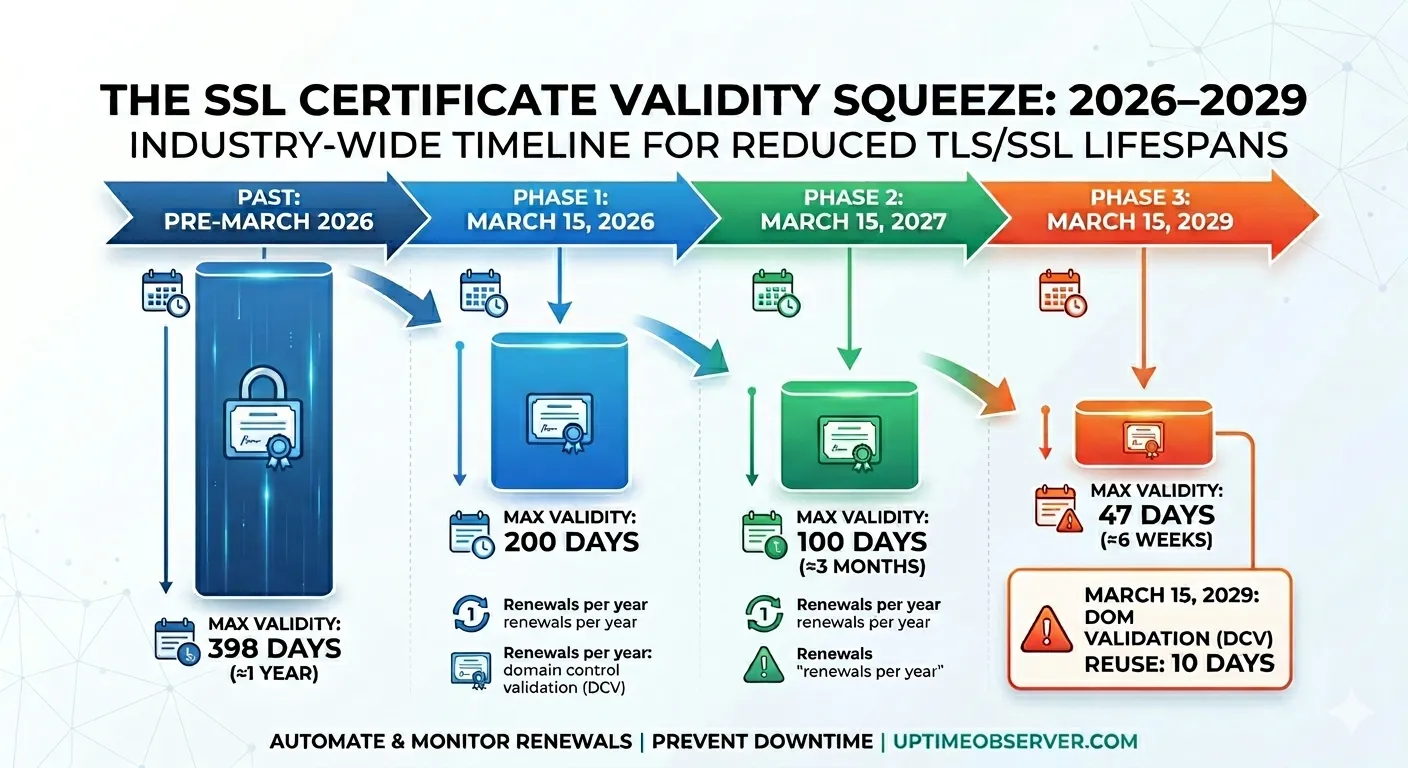
We have entered a phased “step-down” period mandated by the CA/Browser Forum (Ballot SC-081). This isn’t just a minor tweak—it is a complete overhaul of how we maintain web security. By 2029, certificates will expire in less than seven weeks.
The Roadmap: 200, 100, and 47 Days
The industry-wide transition follows a strict timeline. Each milestone reduces the “margin of error” for manual management:
| Effective Date | Max Certificate Validity | Max Domain Validation (DCV) Reuse |
| March 15, 2026 (Active Now) | 200 Days | 200 Days |
| March 15, 2027 | 100 Days | 100 Days |
| March 15, 2029 | 47 Days | 10 Days |
Why the 47-Day Era Changes Everything
For a decade, SSL management was a “once-a-year” task. You could track it on a calendar or a spreadsheet. That approach is now a high-risk gamble for three reasons:
- The “Ghost” Outage: With 47-day lifespans coming in 2029, you will be renewing certificates ~8 times per year. If you manage 10 domains, that’s 80 potential points of failure annually.
- The DCV Crisis: By 2029, your Domain Control Validation (DCV)—the proof that you own the site—will expire every 10 days. This means your automation must not only renew the cert but also successfully re-verify your domain ownership almost weekly.
- No More Safety Net: As we noted in our coverage of Let’s Encrypt ending expiration email alerts, the world’s largest CA is stepping back from manual notifications just as the frequency of renewals is exploding.
3 Steps to Prepare Your Infrastructure
As certificates get shorter, the “window for recovery” shrinks. If a renewal fails on a 47-day certificate, you might only have a few days to fix it before users see a “Your connection is not private” warning. This is now one of the 7 leading causes of downtime that is entirely preventable.
1. Audit Your “Manual” Debt
Any certificate still being handled via a manual CSR (Certificate Signing Request) is a ticking time bomb. Use our Free SSL Expiry Checker to identify which of your current certificates are already on the new 200-day limit.
2. Transition to ACME Automation
You must implement a Certificate Lifecycle Management (CLM) strategy. Protocols like ACME (Automated Certificate Management Environment) are no longer “optional” for modern businesses. As we’ve discussed, cybersecurity is essential for modern businesses, and automation is the only way to scale that security.
3. Monitor the Monitor
Automation scripts fail. Firewalls block validation tokens, and API keys expire. To survive the 47-day era, you need an independent “watcher.” Our SSL Certificate Monitoring service acts as your external fail-safe, alerting you the moment a renewal fails—long before your customers notice.
The Bottom Line
The Bottom Line
The shift to 47-day certificates is about Crypto-Agility. It forces the internet to be faster and more secure. But for the unprepared, it is an express lane to frequent outages.
Don’t let a 47-day window catch you off guard. Start automating and monitoring your certificates today.
Frequently asked questions:
-
Does this change affect my current 1-year SSL certificate?
No. Any certificate issued before March 15, 2026, will remain valid until its original expiration date. However, the moment you renew or reissue that certificate, it will be capped at the new 200-day limit. By March 2027, that limit drops to 100 days.
-
Why is the industry moving to 47-day certificates?
The primary goal is security. Shorter lifespans reduce the "window of opportunity" for hackers to use a stolen private key. It also forces "crypto-agility," ensuring that if a new security vulnerability is found, the entire internet can rotate to new, secure keys within weeks rather than years.
-
Can I still renew my certificates manually?
Technically, yes, but it is no longer practical. In the 47-day era (starting 2029), you would need to manually prove domain ownership and install a new certificate every 6–7 weeks. This significantly increases the risk of human error, which is already one of the leading causes of website downtime.
-
Does this affect Private or Internal CAs?
No. These changes only apply to Publicly Trusted Certificates (those issued by CAs like Let's Encrypt, DigiCert, or Sectigo that browsers automatically trust). Certificates issued by a private, internal CA for corporate intranets can still have longer validity periods.
-
Will I have to pay for my SSL certificate every 47 days?
Most Certificate Authorities are moving to a Subscription Model. You will likely still pay for 1 or 2 years upfront, but the "technical" certificate will automatically swap out every 45–90 days in the background.
-
What happens if my automated renewal fails?
In the old "one-year" model, you had a long time to notice a failure. In the new 47-day model, your Domain Validation might only be valid for 10 days. If the automation fails, your site will show a security warning to users almost immediately.
-
How can I keep track of all these renewals?
As manual alerts from providers become less reliable you need an independent monitoring system. Our SSL Certificate Monitoring tool tracks your expiration dates 24/7 and alerts you via Slack, Email, or SMS the moment a renewal doesn't go as planned.